数学代写| Symmetric Key Systems 代考
离散数学在计算领域有广泛的应用,例如密码学、编码理论、 形式方法, 语言理论, 可计算性, 人工智能, 理论 数据库和软件的可靠性。 离散数学的重点是理论和应用,而不是为了数学本身而研究数学。 一切算法的基础都是离散数学一切加密的理论基础都是离散数学
编程时候很多奇怪的小技巧(特别是所有和位计算相关的东西)核心也是离散数学
其他相关科目课程代写:组合学Combinatorics集合论Set Theory概率论Probability组合生物学Combinatorial Biology组合化学Combinatorial Chemistry组合数据分析Combinatorial Data Analysis
my-assignmentexpert愿做同学们坚强的后盾,助同学们顺利完成学业,同学们如果在学业上遇到任何问题,请联系my-assignmentexpert™,我们随时为您服务!
离散数学代写
$10.4$ Symmetric Key Systems
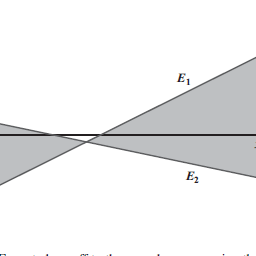
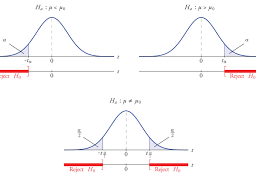
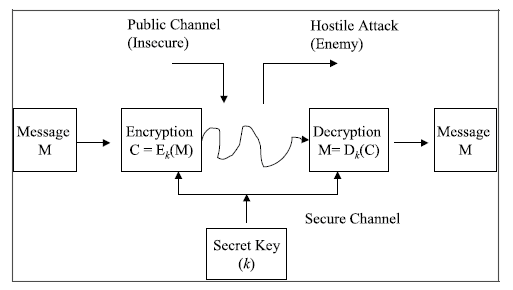
A symmetric key cryptosystem (Fig. 10.6) uses the same secret key for encryption and decryption. The sender and the receiver first need to agree a shared key prior to communication. This needs to be done over a secure channel to ensure that the
$10.4$ Symmetric Key Systems
167
Fig. $10.6$ Symmetric key cryptosystem
shared key remains secret. Once this has been done they can begin to encrypt and decrypt messages using the secret key. Anyone who is able to encrypt a message has sufficient information to decrypt the message.
The encryption of a message is in effect a transformation from the space of messages $\mathscr{l} b$ to the space of cryptosystems $\mathbb{C}$. That is, the encryption of a message with key $k$ is an invertible transformation $f$ such that:
$$
f: \mathscr{M} \rightarrow^{k} \mathbb{C}
$$
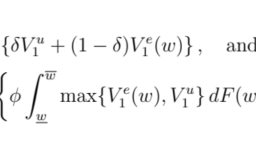
The cipher text is given by $\mathrm{C}=\mathrm{E}{k}(\mathrm{M})$ where $\mathrm{M} \in \mathscr{l} b$ and $\mathrm{C} \in \mathbb{C}$. The legitimate receiver of the message knows the secret key $k$ (as it will have transmitted previously over a secure channel), and so the cipher text $\mathrm{C}$ can be decrypted by the inverse transformation $f^{-1}$ defined by: $$ f^{-1}: \mathbb{C} \rightarrow^{k} \mathscr{M} $$ Therefore, we have that $\mathrm{D}{k}(\mathrm{C})=\mathrm{D}{k}\left(\mathrm{E}{k}(\mathrm{M})\right)=\mathrm{M}$ the original plaintext message.
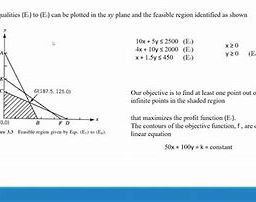
There are advantages and disadvantages to symmetric key systems (Table 10.2), and these include:
Examples of Symmetric Key Systems
(i) Caesar Cipher
The Caesar cipher may be defined using modular arithmetic. It involves a shift of three places for each letter in the plaintext, and the alphabetic letters are represented by the numbers $0-25$. The encyption is carried out by addition (modula 26). The encryption of a plaintext letter $x$ to a cipher letter $c$ is given by $^{3}$ :
${ }^{3}$ Here $x$ and $c$ are variables rather than the alphabetic characters ‘ $x$ ‘ and ‘ $c$ ‘.Table. $10.2$ Advantages and disadvantages of symmetric key systems
\begin{tabular}{|l|l|}
\hline Advantages Encryption process is simple (as the same key is used for encryption and decryption) & Disadvantages A shared key must be agreed between two parties \
\hline It is faster than public key systems & Key exchange is difficult as there needs to be a secure channel between the two parties (to ensure that the key remains secret) \
\hline It uses less computer resources than public key systems & If a user has $n$ trading partners then $n$ secret keys must be maintained (one for each partner) \
\hline It uses a different key for communication with every different party & There are problems with the management and security of all of these keys (due to volume of keys that need to be maintained) \
\hline & Authenticity of origin or receipt cannot be \
& proved (as key is shared) \
\hline
\end{tabular}
$$
c=x+3(\bmod 26)
$$
Similarly, the decryption of a cipher letter $c$ is given by:
$$
x=c-3(\bmod 26)
$$
(ii) Generalized Caesar Cipher
This is a generalisation of the Caesar cipher to a shift of $k$ (the Caesar cipher involves a shift of three). This is given by:
$$
\begin{array}{cl}
f_{k}=\mathrm{E}{k}(x)=x+k(\bmod 26) & 0 \leq k \leq 25 \ f{k}^{-1}=\mathrm{D}{k}(c)=c-k(\bmod 26) & 0 \leq k \leq 25 \end{array} $$ (iii) Affine Transformation This is a more general transformation and is defined by: $$ \begin{gathered} f{(a, b)}=\mathrm{E}{(a, b)}(x)=a x+b(\bmod 26) \quad 0 \leq a, b, x \leq 25 \operatorname{and} \operatorname{gcd}(a, 26)=1 \ f{(a, b)}^{-1}=\mathrm{D}_{(a, b)}(c)=a^{-1}(c-b)(\bmod 26) \quad a^{-1} \text { is the inverse of } a \bmod 26
\end{gathered}
$$
$10.4$ 对称密钥系统
对称密钥密码系统(图 10.6)使用相同的密钥进行加密和解密。发送方和接收方首先需要在通信之前就共享密钥达成一致。这需要通过安全通道完成,以确保
$10.4$ 对称密钥系统
167
图 $10.6$ 对称密钥密码系统
共享密钥仍然保密。完成此操作后,他们可以开始使用密钥加密和解密消息。任何能够加密消息的人都有足够的信息来解密消息。
消息的加密实际上是从消息空间 $\mathscr{l} b$ 到密码系统 $\mathbb{C}$ 空间的转换。也就是说,使用密钥 $k$ 对消息进行加密是一个可逆变换 $f$,使得:
$$
f: \mathscr{M} \rightarrow^{k} \mathbb{C}
$$
密文由 $\mathrm{C}=\mathrm{E}{k}(\mathrm{M})$ 给出,其中 $\mathrm{M} \in \mathscr{l} b$ 和 $\mathrm {C} \in \mathbb{C}$。消息的合法接收者知道密钥 $k$(因为它之前将通过安全通道传输),因此密文 $\mathrm{C}$ 可以通过逆变换 $f^{- 解密1}$ 定义为: $$ f^{-1}: \mathbb{C} \rightarrow^{k} \mathscr{M} $$ 因此,我们有 $\mathrm{D}{k}(\mathrm{C})=\mathrm{D}{k}\left(\mathrm{E}{k}(\mathrm{M} )\right)=\mathrm{M}$ 原始明文消息。
对称密钥系统(表 10.2)有利有弊,包括:
对称密钥系统的例子
(i) 凯撒密码
凯撒密码可以使用模运算来定义。它涉及将明文中的每个字母移动三个位置,并且字母由数字 $0-25$ 表示。加密是通过加法进行的(模 26)。明文字母 $x$ 到密文字母 $c$ 的加密由 $^{3}$ 给出:
${ }^{3}$ 这里的 $x$ 和 $c$ 是变量,而不是字母字符’$x$’和’$c$’.Table。 $10.2$ 对称密钥系统的优缺点
\begin{表格}{|l|l|}
\hline 优点 加密过程简单(加密和解密使用相同的密钥) & 缺点 共享密钥必须由两方商定 \
\hline 它比公钥系统更快,并且密钥交换很困难,因为双方之间需要有一个安全通道(以确保密钥保持秘密)\
\hline 它比公钥系统使用更少的计算机资源 & 如果用户有 $n$ 贸易伙伴,则必须维护 $n$ 密钥(每个伙伴一个)\
\hline 它使用不同的密钥与每个不同的方进行通信&所有这些密钥的管理和安全性都存在问题(由于需要维护的密钥量)\
\hline & 原产地或收据的真实性不能是 \
& 证明(因为密钥是共享的)\
\hline
\end{表格}
$$
c=x+3(\bmod 26)
$$
类似地,密码字母 $c$ 的解密由下式给出:
$$
x=c-3(\bmod 26)
$$
(ii) 广义凯撒密码
这是凯撒密码对 $k$ 移位的概括(凯撒密码涉及到 3 的移位)。这是由以下给出的:
$$
\开始{数组}{cl}
f_{k}=\mathrm{E}{k}(x)=x+k(\bmod 26) & 0 \leq k \leq 25 \ f{k}^{-1}=\mathrm{D}{k}(c)=c-k(\bmod 26) & 0 \leq k \leq 25 \结束{数组} $$ (iii) 仿射变换 这是一个更一般的转换,定义为: $$ \开始{聚集} f{(a, b)}=\mathrm{E}{(a, b)}(x)=a x+b(\bmod 26) \quad 0 \leq a, b, x \leq 25 \operatorname {and} \operatorname{gcd}(a, 26)=1 \ f{(a, b)}^{-1}=\mathrm{D}_{(a, b)}(c)=a^{-1}(cb)(\bmod 26) \quad a^{ -1} \text { 是 } a \bmod 26 的倒数
\结束{聚集}
$$
图论代考
自然数 $\mathbb{N}$ 由数字 $\{1,2,3, \ldots\}$ 组成。整数 $\mathbb{Z}$ 由 $\{\ldots-2,-1,0,1,2, \ldots\}$ 组成。有理数 $\mathbb{Q}$ 由 $\left\{{ }^{p} /_{q}\right.$ 形式的所有数字组成,其中 $p$ 和 $q$ 是整数,$ \left.q \neq 0\right\}$。实数 $\mathbb{R}$ 被定义为有理数收敛序列的集合,它们是有理数的超集。它们包含有理数和无理数。复数 $\mathbb{C}$ 由 $\{a+bi$ 形式的所有数字组成,其中 $a, b \in \mathbb{R}$ 和 $i=\sqrt{-} 1\}美元。 毕达哥拉斯三元组(图 3.2)是满足毕达哥拉斯方程 $x^{2}+y^{2}=z^{2}$ 的三个整数的组合。有无数个这样的三元组,这种三元组的一个例子是 $3,4,5$,因为 $3^{2}+4^{2}=5^{2}$。 毕达哥拉斯学派发现了音乐和数字之间的数学关系,他们的哲学是数字隐藏在从音乐到科学和自然的一切事物中。这导致了他们的哲学,即“一切都是数字”。
数学代写| DISCRETE MATHEMATICS代考 请认准UprivateTA™. UprivateTA™为您的留学生涯保驾护航。
抽象代数代考
抽象代数就是一门概念繁杂的学科,我们最重要的一点我想并不是掌握多少例子。即便是数学工作者也不会刻意记住Jacobson环、正则环这类东西,重要的是你要知道这门学科的基本工具和基本手法,对概念理解了没有,而这一点不需要用例子来验证,只需要看看你的理解和后续概念是否相容即可。
矩阵论代考matrix theory
数学,矩阵理论是一门研究矩阵在数学上的应用的科目。矩阵理论本来是线性代数的一个小分支,但其后由于陆续在图论、代数、组合数学和统计上得到应用,渐渐发展成为一门独立的学科。
密码学代考
密码学是研究编制密码和破译密码的技术科学。 研究密码变化的客观规律,应用于编制密码以保守通信秘密的,称为编码学;应用于破译密码以获取通信情报的,称为破译学,总称密码学。 电报最早是由美国的摩尔斯在1844年发明的,故也被叫做摩尔斯电码。
- Cryptosystem
- A system that describes how to encrypt or decrypt messages
- Plaintext
- Message in its original form
- Ciphertext
- Message in its encrypted form
- Cryptographer
- Invents encryption algorithms
- Cryptanalyst
- Breaks encryption algorithms or implementations
编码理论代写
编码理论(英语:Coding theory)是研究编码的性质以及它们在具体应用中的性能的理论。编码用于数据压缩、加密、纠错,最近也用于网络编码中。不同学科(如信息论、电机工程学、数学、语言学以及计算机科学)都研究编码是为了设计出高效、可靠的数据传输方法。这通常需要去除冗余并校正(或检测)数据传输中的错误。
编码共分四类:[1]
数据压缩和前向错误更正可以一起考虑。